U.S. Customs Isn’t Protecting Traveler Data After Electronic Searches
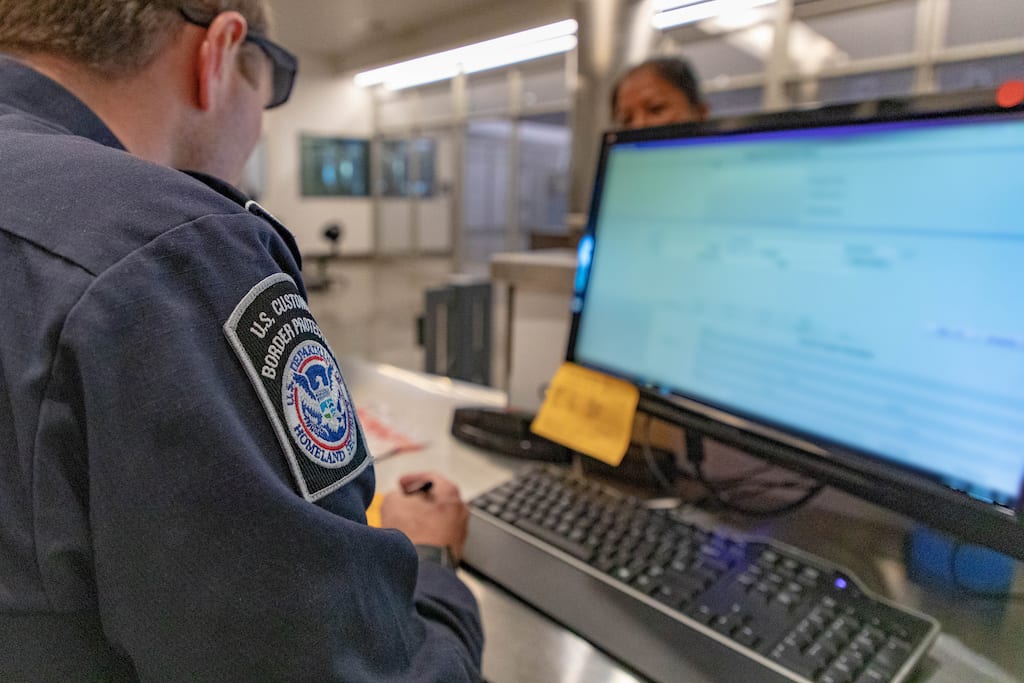
Photo Credit: A customs officer at a border crossing in California. U.S. Customs and Border Protection Office of Public Affairs Visual Communications Division / Mani Albrecht
Skift Take
It should come as no surprise that the government isn't following its own rules when it comes to securing the traveler data it seizes from personal devices. Another reminder to take precautions, even if your chance of getting searched is rather low.


