Hacking In-Flight Entertainment Is Harder Than Hackers Would Have You Believe
Skift Take
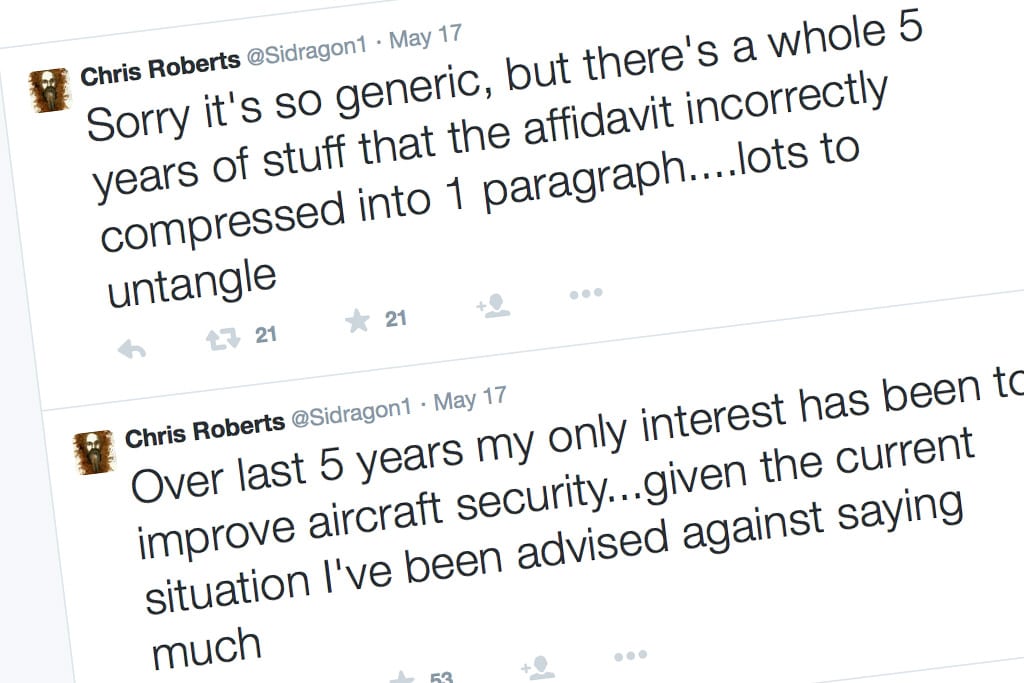
Tweeting threats from inside an aircraft is not a way to prove you have what it takes to keep aviation safe. But anyone with two fingers of sense knows that.
For better or worse, hacker Chris Roberts has made a name for himself as that guy who hacked in-flight entertainment (IFE) systems and claimed to make his plane fly sideways.
Industry experts question the validity of his claims to access the engine control systems, because the systems in question are not connected to the same networks that control the IFE he allegedly exploited. Both Airbus and Boeing indicate that their so-called wireless cockpit systems are isolated from the networks for in-flight connectivity and in-flight entertainment. As an Airbus spokesperson told us when we asked:
“What the passengers use on board uses a totally different network to what the pilots may use in the cockpit. The cockpit system would also utilize a completely different transmitter/hotspot with a different radio frequency band. In short, they’re completely segregated – including: different hardware; different hotspot; different fre


